How to secure your internet browsing experience?
– Rawad Mallah –

Securing your private information when surfing the web is always essential, especially when it comes to accessing gay websites. This task does not depend only on using fake names, photos … but the Web Browser (Internet Explorer, Google Chrome, and others), Operating System (Windows and programs installed), and the Tools (Computer, cell phone, tab etc.) in use.
The Risks
- People gaining access to your online activity if you are using an unsecured or illicit wireless network.
- Theft of personal information from, or access to browsing history on public computers.
- Malware, including spyware and keystroke loggers, on public and private computers.
- ‘Shoulder surfing’ – people viewing your screen.
Using a Public WIFI
The main security risk associated with using your own device in a public place, is that the WiFi may not be secured, enabling unauthorized people to intercept anything you are doing online. This could include capturing your passwords and reading private emails. This can happen if the connection is not encrypted between your device and the WiFi. Alternatively, you may simply be prompted to log in to enable Internet access. This will tell the operator that you are online in their café, hotel or pub.
With an encrypted connection, you will be required to enter a ‘key’, which may look something like 1A648C9FE2.
Using a Public Computer

Most of us will occasionally have to use a public computer for one reason or another. Unfortunately, using public computers carries an inherent risk of exposing personal data. Here are some things you can do to protect yourself and lessen that risk.
- Always Browse the web in private mode:
Most modern Web Explorers include an option to surf the web privately; this will delete all activity done upon exit from Browsing History, Saved password and Temporary files. To access this option in IE got to “Tools > safety > InPrivate Browsing”. In Mozilla Firefox go to “Menu > New Private Window”. In Google Chrome go to “Menu > New Incognito Window”.
- Don’t save files locally:
Many of the files you would normally save locally, such as e-mail attachments, can contain private or sensitive information. An easy way to protect this data is to carry a flash drive and save files there when necessary. It is also a good idea to attach the flash drive to your key ring so you will be less likely to misplace it and create a new security problem.
- Don’t do online banking or enter credit card information:
You should remember that ultimately, a public computer is never going to be anywhere close to completely secure, so there are some things you just should not use them for. If you really need to check your balance on the road, you are much better off finding a branch office or ATM or using your phone. Even your purchases from eBay or Amazon.com can and should wait until you can browse from a more secure location. A little added convenience is not worth the trouble of having your credit card hijacked.
- Reboot:
When you are finished using the public computer, the final thing you should do is a hard reboot. This will not only clear the page file, if you have enabled that option, but it will also clear out everything you did from the physical memory (RAM).
- Pay attention to your surroundings and use common sense:
Finally, you need to remember to pay attention to things outside of the actual computer that could be a risk. Be aware of strangers around you (potential shoulder surfers) and remember that a public computer is just that — public. Do not view any truly sensitive documents you could not bear for others to see. Remember the security camera over your shoulder. Cover your hands from view when entering any login information to prevent any casual spying.
Most important, remember that there is nothing you can do to make a public computer completely secure. A truly malicious owner or user could install a hardware keystroke logger that would be impossible to detect without actually opening the case and inspecting it. With that less-than-comforting thought, use common sense and use public computers only for insensitive tasks.
Using a Private Computer
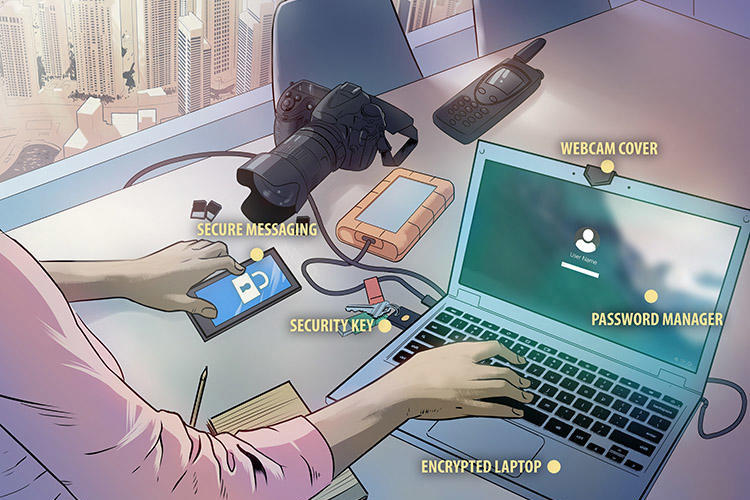
There are several habits that you should develop to improve the security of your online activities. While the following list may seem like a lot to manage, most of these recommendations are simple and following them will significantly bolster your browsing security.
- Keep your browser software up-to-date: This is crucial, as new patches are often released to fix existing vulnerabilities in browser software. This recommendation does not apply solely to browser software – it is critical to keep the operating system software and any other software you have up-to-date for the same reason.
- Run anti-virus software: Anti-virus software provides protection by scanning for and removing malicious files on your computer. There are many excellent options for virus protection software (both paid and free). For added security, update your anti-virus program to an Internet security program. An Internet security program will always add a higher layer of protection as it integrates an Anti-virus, Anti-spyware, spam filter, firewall and a lot of other features.
- Scan files before downloading: It is important to avoid downloading anything until you are confident that it is secure. If you have any suspicion that a file may not be legitimate or may be infected, scan it with antivirus software before downloading.
- Install Only Trusted Programs: It may seem obvious but only download software or programs from known, trusted sources. A surprising number of Internet users download free programs from unknown sources and inadvertently install damaging spyware or viruses onto their computers. If you are unsure about a particular program, do some research online; chances are if it is not a legitimate program or application, you will not be able to verify it online.
- Install only trusted Extensions: Extensions or add-ons are pieces of software that add or modify a feature or functionality in your web browser. Some of them allow you to block ads, watch online videos or they are closely integrated in social media websites improving your online session. For example, Adobe Flash is an add-on that allows your web browser to watch movies or play online games. The possible issues, which may appear from extensions, is that some of them can be used to inject ads into the sites you visit or track your entire browsing activity, being therefore used for malicious purposes.
- Watch out for phishing: Phishing attacks use online communications (usually email) to trick users into giving out their sensitive information. Often times these messages appear to be from banks, social media sites, shopping sites, or payment processers. Phishing messages frequently contain links that lead to counterfeit versions of popular sites. You can avoid falling victim to phishing schemes by ignoring unsolicited messages and not clicking on hyperlinks or attachments in emails (type or copy/paste the URL as it appears instead).
- Do not reuse passwords: Using the same password for multiple sites only makes it easier for attackers to compromise your sensitive information. Instead, keep track of your different passwords with a handwritten list that you keep in a safe place or come up with your own algorithm for creating unique passwords that only you would know. It is also recommended that you change your passwords every 90 days.
- Use HTTPS: The “s” in “https” stands for secure, meaning that the website is employing SSL encryption. Check for an “https:” or a padlock icon in your browser’s URL bar to verify that a site is secure before entering any personal information.
- Read privacy policies: Websites’ privacy policies and user agreements should provide details as to how your information is being collected and protected as well as how that site tracks your online activity. Websites that do not provide this information in their policies should generally be avoided.
- Regularly monitor your bank statements: Keeping an eye on your online statements will allow you to react quickly in the event that your account has been compromised.
- Disable stored passwords: Nearly all browsers and many websites in general offer to remember your passwords for future use. Enabling this feature stores your passwords in one location on your computer, making them easier for an attacker to discover if your system is compromised. If you have this feature enabled, disable it and clear your stored passwords.
- Turn on your browser’s popup blocker: Popup blocking is now a standard browser feature and should be enabled any time you are surfing the web. If it must be disabled for a specific program, turn it back on as soon as that activity is complete.
Following these 13 tips will go a long way in protecting you from attackers, malware, and many of the other threats like personal information theft that we all face online.

Sources
http://www.techrepublic.com/blog/10-things/10-things-you-should-do-to-protect-yourself-on-a-public-computer/
http://internet-browser-review.toptenreviews.com/surf-safely-how-to-secure-your-browser-and-protect-your-computer.html


